Tech
How to Detect and Remove Keyloggers on a Mac?

Keyloggers in general fall into two distinct categories, being either those who someone installed for control purposes or those who are malware and used for snooping. Either way, it is always possible to remote keyloggers on a Mac, with the difficulty depending on the method.
There are four categories of keyloggers:
- Hardware
- Software
- Keyboard
- Malware
And while most people are focused on the last category because it is always unwanted, there might be good reasons to check for others as well. In many cases, a workplace or even a laptop sales location might want to install keyloggers to collect data on their workers or customers.
In some cases, you will be required to add a keylogger to your own device as part of a working agreement. In others, this will be malware added by someone else and without your knowledge.
Thankfully, if you want to remove keylogger software and hardware, there is always a way to do so. Some are more drastic, but none are impossible.
Hardware vs. Software
In the terms of cybersecurity, especially if we are talking about a Mac laptop or desktop, we usually mean the software variety of keyloggers. These are either legitimate software or malware, but are vastly more common than someone hacking your magic keyboard.
But, and this is especially the case for devices with public access, there can be keyboards stripped with attachments meant to log what you are typing without ever accessing the device you are typing on.
These are usually visible. And, even in cases where they are made as firmware to the keyboard itself, it is usually relatively cheap to simply exchange the keyboard. Alternatively, it can be created by changing the software input type from QWERTY to Dvorak or AZERTY, thus basically scrambling the results.
With software, the issue is easier to notice, as the keylogger will use system resources. But, if the infection is very deep it is possible that few things will save you short of a full system reset.
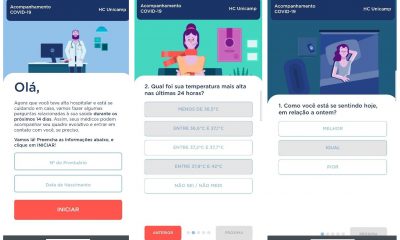
Monitors and Trackers
Keylogger monitors are more common than you think. Even places like Upwork use them to show the work the freelancers are doing, with their knowledge, of course.
If you believe that your Mac is affected, select ‘’Go’’ from the dock and search up ‘’Utilities’’ where the activity monitor will be available. Here you will see the processes where everything that currently uses system resources will be listed.
If you notice any strange program here that you believe is a keylogger you can end it and it will end the program. Trackers will work in the same way, and even use more resources, making them easier to notice.
If you don’t know if something is a keylogger, you can always search up a suspicious name online as the list of such software is frequently updated.
Remove Keyloggers that are Malware
This is easier than it seems, as most types of security software will notice keyloggers quite quickly. But, for this you need to be certain that your anti-virus and your OS are up to date and that they have lists of all the newest signatures.
Running a complete scan will almost always show the malware and ask you to remove it. If you are using wanted keylogger software at these times be sure to disable it.
If you believe that using the device while your keystrokes are logged might be problematic to even attempt something, you can always use the Mac option for a software keyboard, or even Voice to Text options that would jump over the keyboard.
That way you can use all of the software to deal with the possible infection without ever tipping off the person that might be snooping around your Mac, physically or digitally.
Clean Slate
In the case that you have a software problem that is hard or impossible to solve, you can always make a clean slate and remove everything you don’t need, or want.
Make a backup of all of your files that you want to keep and go to ‘’Disk Utility’’ to choose the option to erase everything. Once that is done, you can reinstall Mac OS to the device and use it normally, sourcing your data from the backup.